Creating a Secure BYOD Policy for Laptops that Employees Will Actually Follow
In today’s rapidly evolving digital landscape, organizations must adapt to new threats and emerging technologies without breaking the bank. ...
Read More
Making the Transition from VDI to a Secure BYOD Solution
Remote work’s growing popularity has created an increased demand for secure remote connectivity solutions. However,...
8 Questions to Help you Build Your Secure BYO-PC Program
The growing use of BYOD (Bring Your Own Device) and BYO-PC (Bring Your Own PC)...

Extending MDM to Laptops: How to Enable Secure BYO-PC for Remote Work
With an increasingly mobile workforce, employees have come to expect flexibility. They want flexibility with...
Get Our Latest Blogs Straight to Your Inbox

Ensuring Data Security When Employees Work Remotely
Remote work skyrocketed out of necessity during the pandemic. Pew Research Center reports that the...
Venn Software named as a Sample Vendor for BYOPC Security in two Gartner® Hype Cycles™
Venn Software named as a Sample Vendor for BYOPC Security in the Gartner® Hype Cycle™...

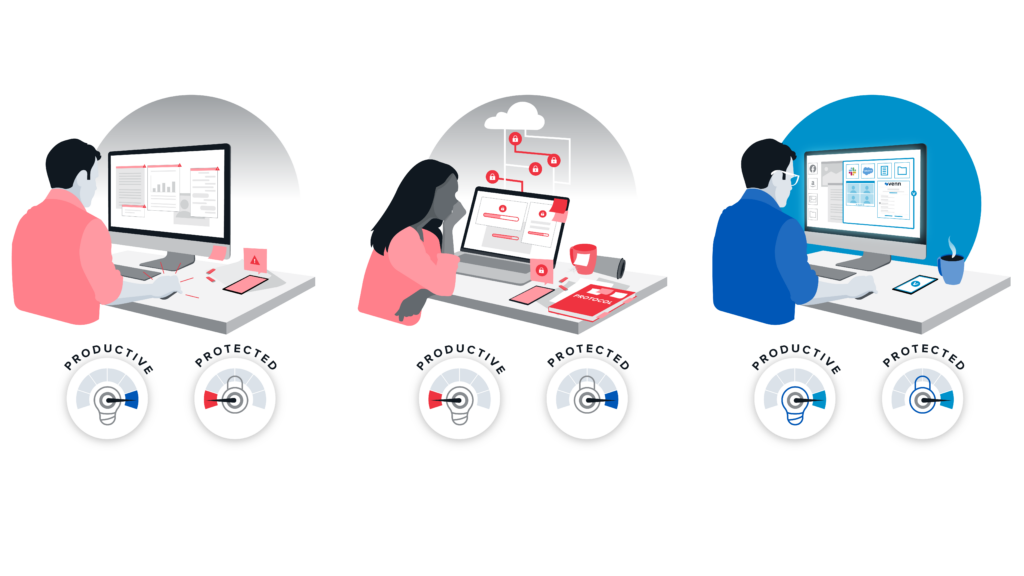
The future of work is hybrid: What does this model look like and what are the implications for security?
There’s no doubt that the hybrid work arrangement is here for the long haul. It’s...

7 Must-Have Remote Work Software Features for Optimal Operational Efficiency
Working from home has become a new normal and with it comes the need for...
Venn is Changing the Virtual Desktop Game
The new realities of modern work have eroded the promise of Virtual Desktop Infrastructure (VDI)...

How to Improve Your DLP With Accurate Data Organization
As organizations continue to expand their global networks by collaborating and communicating with employees and...